Authorized API Testing
Modern API Security Testing
We assess REST APIs, backend services, authentication mechanisms, authorization logic, endpoint exposure, data handling, and integration risks. Our API testing identifies weaknesses such as broken object-level authorization, excessive data exposure, insecure authentication, rate limiting gaps, and misconfigured endpoints.
Built for modern applications, our engagements help businesses reduce real-world risk through structured testing, clear reporting, and practical remediation guidance.
Why it matters
- Protect sensitive business logic and customer data
- Validate authentication, authorization, and rate limiting
- Reduce exposure across integrations and backend services
Related Service
Explore all cybersecurity services
Review Enverties Technologies service offerings, including authorized penetration testing, cloud security, mobile security, and red team assessments.
What We Test
Coverage across modern API environments
Our API security engagements focus on the controls that protect sensitive business logic, customer data, and service integrations across modern applications and distributed environments.
Authentication and access control
Review token handling, session controls, object-level authorization, role enforcement, and identity validation across exposed endpoints.
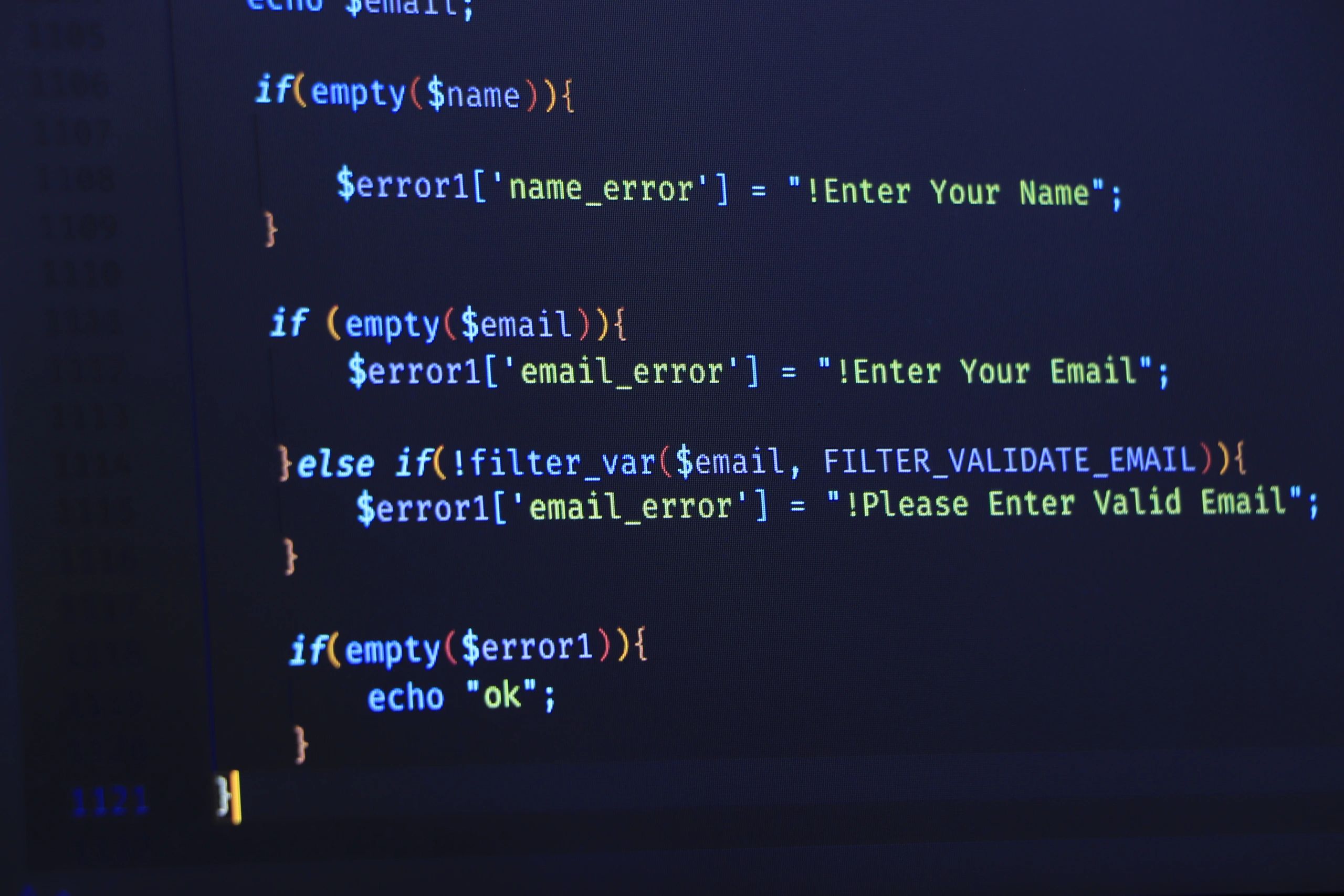
Data exposure and endpoint security
Identify excessive data exposure, insecure methods, weak input validation, missing rate limits, and misconfigured API routes.
Integration and backend trust
Assess third-party connections, backend trust assumptions, service-to-service communication, and exposed business logic.
Coverage
Key Testing Areas
We combine manual validation and targeted attack simulation to uncover exploitable weaknesses that affect API confidentiality, integrity, and availability.
Broken object authorization
Test for unauthorized access to records, resources, and functions through predictable identifiers and weak access checks.
Authentication weaknesses
Assess login flows, token lifecycle, credential handling, and session security for exploitable gaps.
Rate limiting gaps
Evaluate abuse resistance, brute-force protections, throttling controls, and denial-of-service exposure.
Input validation flaws
Check for injection risks, unsafe deserialization, parameter tampering, and insecure request handling.
Sensitive data exposure
Review responses, error handling, and logging behavior for leakage of secrets, PII, and internal details.
Integration risks
Assess third-party connections, backend trust assumptions, and insecure service-to-service communication.
Our Approach
Structured testing with practical outcomes
We begin by understanding the API architecture, authentication model, exposed endpoints, and business workflows in scope. Testing is then performed through a combination of manual validation and targeted attack simulation to identify exploitable weaknesses.
Our team prioritizes issues by business impact and technical risk, then provides practical remediation guidance to help internal teams strengthen controls and reduce exposure.
Deliverables
- Executive and technical reporting
- Evidence-backed findings with reproducible context
- Prioritized remediation guidance
- Support for validation and follow-up discussions
